Spam mails have evolved since the first one was sent back in 1978. Its evolutions span from the techniques, tactics, and the latest trends cybercriminals piggyback on to make it more legitimate-looking and urgent-sounding – an effective formula to prey upon an unsuspecting user.
One of Kaspersky’s elite researchers, Noushin Shabab, probed into the spam threat landscape in Asia Pacific (APAC) this year to answer – what if emails do not get opened?
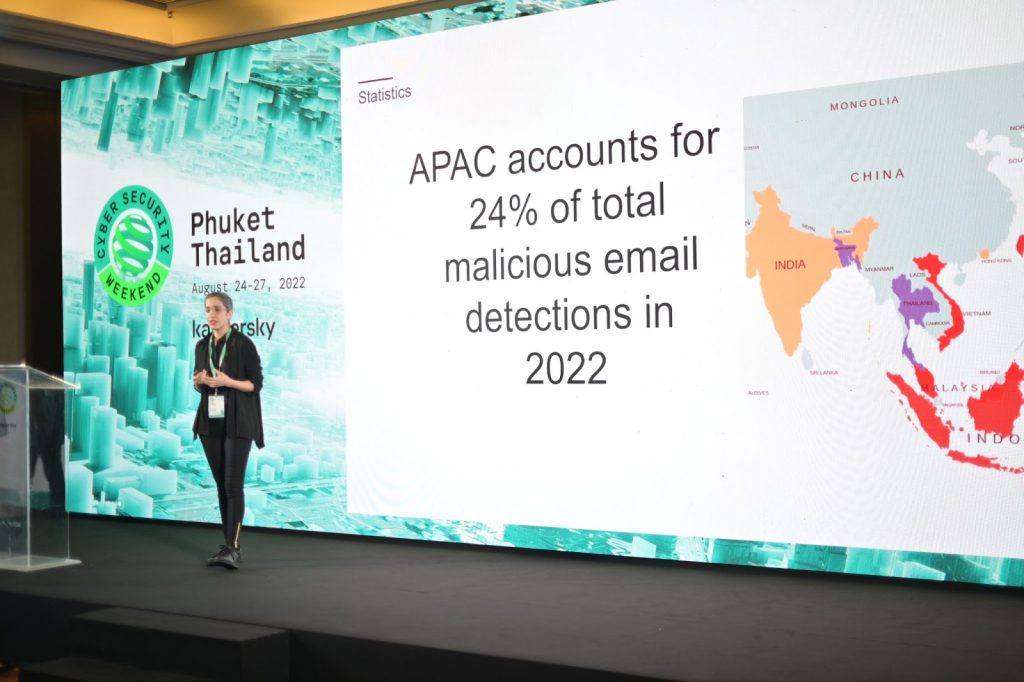
Shabab, presented in front of selected media from the region during Kaspersky’s 8th APAC Cyber Security Weekend, revealed that the region received 24% of the global malicious spam mails being detected and blocked by Kaspersky solutions. This means one in four junk electronic messages were delivered to computers in APAC.
Noushin Shabab, Senior Security Researcher for Global Research and Analysis Team (GReAT) at Kaspersky
Malicious spam is not a technologically complex attack, but when done with sophisticated social engineering techniques, it poses a severe threat to individuals and enterprises alike. These junk mails are sent out in mass quantities by spammers and cybercriminals who are looking to do one or more of the following:
- Make money from the small percentage of recipients that actually respond to the message
- Run phishing scams – in order to obtain passwords, credit card numbers, bank account details, and more
- Spread malicious code onto recipients’ computers
In 2022, more than half (61.1%) of the malicious spam detected in the region targeted Kaspersky users from Vietnam, Malaysia, Japan, Indonesia, and Taiwan.
Shabab cited three main factors which cause the bulk of spam emails targeting APAC —- its population, the high adoption of e-services, and the pandemic lockdowns.
The APAC region has almost 60% of the world’s population and this means that there are more potential victims for scammers here compared to other parts of the world. The extensive use of online services such as online shopping and other online platforms for day-to-day activities here also makes individuals more susceptible to falling victim to scams. There is also the lingering pandemic aftermath which led to lockdowns and work-from-home set up in the region where people took their work computers home. Home networks are usually less protected from cyberattacks.
“Since 2018, the number of malicious spam mails detected by our solutions has seen a gradual decline after its peak in 2019. This, however, does not equate to our mailboxes being cleaner and safer. Our constant monitoring of the current and new Advanced Persistent Threats (APTs) operating in Asia Pacific showed that majority of these notorious threat actors use targeted phishing called spear phishing to crack into an organization’s systems,” reveals Noushin Shabab, Senior Security Researcher for Global Research and Analysis Team (GReAT) at Kaspersky.
The most recent example of an APT targeting key entities in APAC through sophisticated malicious mails is the “Sidewinder” threat actor. Since October 2021, the Sidewinder threat actor has been using new malicious JS code with recently created C2 server domains. The attacker, also known as Rattlesnake or T-APT4, targets victims with spear-phishing emails containing malicious RTF and OOXML files.
Known for targeting military, defense and law enforcement agencies, foreign affairs, IT, and aviation entities in Central and South Asia, Sidewinder is considered one of the most prolific threat actors monitored in the APAC region. Kaspersky experts also recently found spear phishing documents which appear to be aimed at future targets in Singapore.
Some of the main characteristics of this threat actor that make it stand out among the others are the sheer number, high frequency and persistence of their attacks, and the large collection of encrypted and obfuscated malicious components used in their operations. Kaspersky experts, who have been monitoring Sidewinder since 2012, have detected over a thousand spear phishing attacks by this APT actor since October 2020.
Sidewinder also continues to expand its victimology and to sharpen its phishing tactics.
For instance, to reduce the suspicion raised by some of their spear-phishing documents that had no text content, the group followed their first attempt to attack the victim – a spear-phishing email containing a malicious RTF exploit file – with another similar email, but in this case, the title of the malicious document was “_Apology Letter.docx”, and it contained some text explaining that the previous email was sent in error and that they are reaching out to apologize for that mistake.
“There are many more well-oiled APT groups like Sidewinder who are constantly upgrading their tools and tactics to target high-profile victims in APAC through believable spam and phishing emails. The implication for enterprises and government organizations here is that a single malicious email when clicked can crumble your most sophisticated defenses, and usually, APTs like Sidewinder just need one door to open, one machine to infect, and then it can hide and stay undetected for long,” Shabab adds.
APTs target any sensitive data; one doesn’t need to be a government agency, major financial institution, or energy company to become a victim.
The major danger of APT attacks is that even when they are discovered and the immediate threat appears to be gone, the hackers may have left multiple backdoors open that allow them to return when they choose. This increases the importance of guarding mailboxes – an entry point they usually exploit to get a foothold of an organization’s networks.
Employees across all ranks need to be aware of the threats, such as the possibility of bogus emails landing in their inboxes. Besides education, technology that focuses on email security is necessary.
To be able to search for potential spear-phishing signs without diminishing the company’s actual security, Kaspersky suggests private and public companies to install protective anti phishing solutions on mail servers as well as on employee workstations.
Enterprises should also utilize advanced security software that can detect sophisticated APT attacks.
For governments, Shabab suggests defining better spam regulations to curb spam risks. “Fewer spam emails from legitimate organizations means people are less used to receiving unexpected emails every day and are more vigilant when they are being targeted with malicious spear phishing emails,” she adds.
About Kaspersky
Kaspersky is a global cybersecurity and digital privacy company founded in 1997. Kaspersky’s deep threat intelligence and security expertise is constantly transforming into innovative security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe. The company’s comprehensive security portfolio includes leading endpoint protection and a number of specialized security solutions and services to fight sophisticated and evolving digital threats. Over 400 million users are protected by Kaspersky technologies and we help 240,000 corporate clients protect what matters most to them. Learn more at www.kaspersky.com.